Introduction to Autonomous Threat Detection
What Is Autonomous Threat Detection?
Imagine a security guard who never sleeps, never blinks, and learns from every single incident. That’s what autonomous threat detection systems aim to be. They monitor networks, systems, and user behavior automatically—and make decisions without waiting for human input.
Instead of reacting after damage is done, these systems predict, detect, and respond in real time. Smart, right?
Why Traditional Security Systems Fall Short
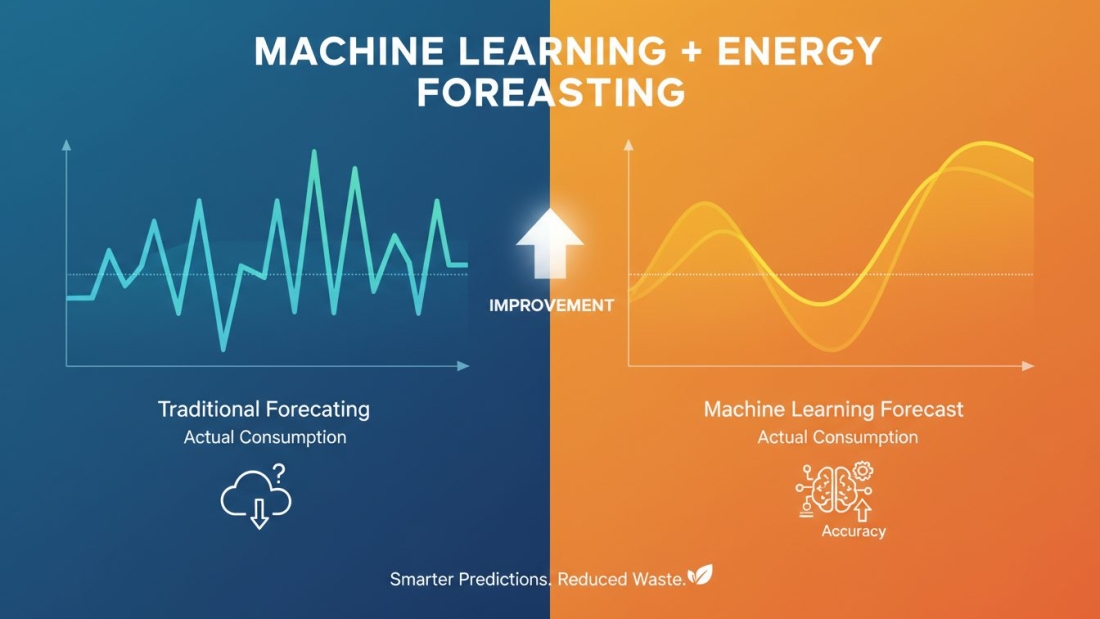
Traditional security relies on rule-based systems. If X happens, trigger Y alert. Sounds simple—but hackers don’t follow rules. They evolve.
Static rules can’t keep up with zero-day attacks, insider threats, or subtle behavioral anomalies. It’s like using a checklist to catch a master thief. You’ll miss something.
That’s where machine learning steps in.
The Rise of Machine Learning in Cybersecurity
From Rule-Based Systems to Intelligent Models
Machine learning (ML) flipped the script. Instead of telling systems what to look for, we let them learn patterns from data.
Think of it like teaching a dog tricks versus letting it observe and adapt on its own. ML models study massive datasets, detect patterns, and identify deviations that humans might overlook.
Key Benefits of Machine Learning in Threat Detection
- Detects unknown threats
- Reduces manual monitoring
- Learns continuously
- Adapts to evolving attack techniques
It’s proactive security, not reactive defense.
Core Components of an Autonomous Threat Detection System
Building such a system isn’t magic. It’s architecture, data, and strategy.
Data Collection and Integration
Everything starts with data. Logs, user activity, network packets, endpoint behavior—you name it.
Without quality data, your ML model is blind.
Data Preprocessing and Feature Engineering
Raw data is messy. You need to clean it, normalize it, and transform it into meaningful features.
Garbage in, garbage out. Always.
Model Selection and Training
Different problems require different models. Classification? Anomaly detection? Prediction?
You choose wisely—and train with labeled or unlabeled data.
Deployment and Monitoring
Once trained, the model is deployed into production. But that’s not the end. Continuous monitoring ensures it stays accurate over time.
Types of Machine Learning Used in Threat Detection
Supervised Learning
Here, models train on labeled datasets. You tell the system what’s malicious and what’s normal.
Best for:
- Malware classification
- Spam detection
Unsupervised Learning
No labels. The model identifies anomalies on its own.
Perfect for detecting unknown threats.
Semi-Supervised Learning
A mix of both. Useful when labeled data is limited—which is often the case in cybersecurity.
Reinforcement Learning
The system learns by trial and error. It optimizes responses based on rewards and penalties.
Think autonomous incident response.
Designing the Data Pipeline
Log Aggregation
Security logs come from everywhere—servers, firewalls, applications.
Centralizing them is crucial.
Real-Time Streaming vs Batch Processing
Real-time systems detect threats instantly. Batch processing analyzes trends over time.
Choosing the Right Architecture
Cloud-native? On-prem? Hybrid?
The architecture should align with your scalability and compliance needs.
Feature Engineering for Threat Detection
Behavioral Features
Login frequency, session duration, unusual access times.
Patterns matter.
Network-Based Features
Packet size, IP reputation, unusual traffic spikes.
Anomalies scream danger.
User Activity Patterns
Insider threats are tricky. Behavioral analytics helps catch them early.
Model Evaluation and Performance Metrics
Precision and Recall
Precision: How many detected threats are actually threats?
Recall: How many real threats did you catch?
Balance is key.
ROC-AUC and F1 Score
These metrics evaluate model performance across thresholds.
High scores = better detection capability.
Handling False Positives and Negatives
Too many false positives? Alert fatigue.
Too many false negatives? Disaster.
Optimization is critical.
Automating Response Mechanisms
Incident Classification
Once detected, classify severity.
Critical? Medium? Low?
Automated Mitigation Strategies
Block IPs. Disable accounts. Isolate endpoints.
Fast response limits damage.
Challenges in Building Autonomous Systems
Data Imbalance
Threat data is rare compared to normal data. Models may become biased.
Adversarial Attacks
Hackers try to fool ML models. Yes, even AI gets attacked.
Model Drift
Over time, patterns change. The model’s accuracy may drop.
Continuous retraining is necessary.
Scalability and Cloud Deployment
Leveraging Cloud Infrastructure
Cloud platforms provide scalability and processing power.
Ideal for big data environments.
Microservices and Containerization
Using containers improves flexibility and deployment speed.
Think modular and scalable.
Ensuring Explainability and Transparency
Why Explainable AI Matters
Security teams need to know why a threat was flagged.
Blind trust isn’t enough.
Tools for Model Interpretability
SHAP values, LIME, and other explainability tools help uncover model reasoning.
Transparency builds confidence.
Compliance and Ethical Considerations
Data Privacy Regulations
Systems must comply with regulations like GDPR and other privacy laws.
Security should never violate privacy.
Ethical AI in Security
Bias in AI models can create unfair targeting.
Responsible design is non-negotiable.
Continuous Learning and System Improvement
Feedback Loops
Security analysts validate alerts. Their feedback improves models.
Retraining Strategies
Scheduled retraining ensures the system adapts to new threats.
Autonomy doesn’t mean stagnation.
Real-World Use Cases
Intrusion Detection Systems
ML enhances IDS by identifying sophisticated attack patterns.
Fraud Detection Platforms
Banks use ML to detect suspicious transactions instantly.
Endpoint Security Solutions
Detecting ransomware behavior before encryption spreads.
Future Trends in Autonomous Threat Detection
AI-Driven SOCs
Security Operations Centers powered by AI reduce manual workload.
Federated Learning in Cybersecurity
Models learn from decentralized data without sharing raw data.
Privacy meets intelligence.
Conclusion
Building autonomous threat detection systems using machine learning isn’t just a tech upgrade—it’s a survival strategy. Cyber threats evolve every day. Static defenses crumble.
Machine learning offers adaptability, speed, and intelligence. But it’s not plug-and-play. It requires quality data, careful model design, continuous monitoring, and ethical consideration.
Think of it like building a digital immune system. It must learn, adapt, and respond—without harming the body it protects.
The future of cybersecurity? Autonomous, intelligent, and always learning.