A threat intelligence report based on research conducted by PhishReaper and presented by LogIQ Curve
Introduction
Digital payment platforms have transformed financial access across emerging markets, but their popularity has also made them prime targets for sophisticated phishing campaigns. Cybercriminals increasingly exploit trusted fintech brands to deceive users, harvest credentials, and conduct financial fraud.
As the Exclusive OEM Partner of PhishReaper in Pakistan, LogIQ Curve is pleased to share the latest cybersecurity intelligence uncovered by the PhishReaper research team. Through this collaboration, LogIQ Curve introduces the advanced phishing-detection capabilities of the PhishReaper platform to enterprises, financial institutions, telecom operators, and government organizations seeking proactive protection against modern cyber threats.
Organizations interested in strengthening their defenses against phishing infrastructure are encouraged to contact our cybersecurity specialists at security@logiqcurve.com.
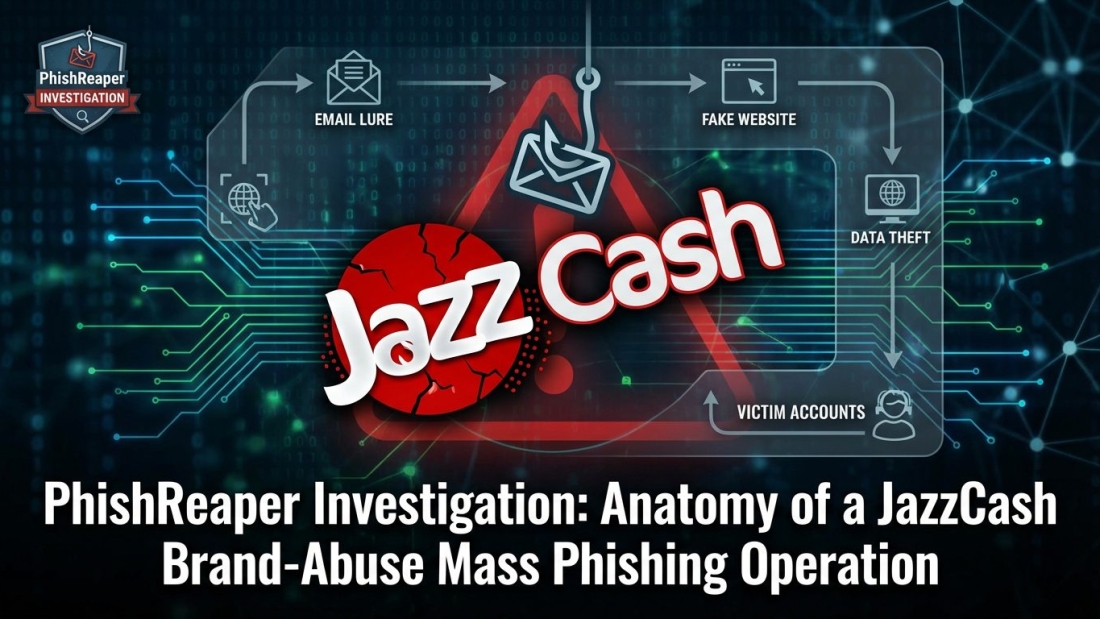
In one such investigation, PhishReaper analyzed a large-scale phishing campaign abusing the brand identity of JazzCash, a widely used mobile wallet platform in Pakistan. The campaign revealed a coordinated mass-phishing operation designed to impersonate the payment service and lure victims into fraudulent digital environments. (PhishReaper)
The Discovery: A Coordinated JazzCash Phishing Campaign
During routine threat-hunting operations, PhishReaper detected infrastructure associated with domains impersonating JazzCash services.
These malicious environments were crafted to replicate the appearance and functionality of legitimate JazzCash interfaces. Such phishing pages often encourage users to:
• Verify account information
• Update payment credentials
• Claim promotional rewards
• Authenticate their mobile wallet accounts
Once victims enter sensitive information, attackers can capture credentials and potentially gain unauthorized access to financial accounts.
The investigation revealed that the phishing activity was not limited to a single website. Instead, it appeared to be part of a coordinated mass-phishing campaign supported by multiple infrastructure components, suggesting a structured operation rather than an isolated incident. (PhishReaper)
Understanding the Infrastructure Behind the Attack
PhishReaper’s analysis examined the infrastructure supporting the JazzCash phishing ecosystem.
Several characteristics indicated an organized phishing operation:
• Domain registrations designed to mimic legitimate JazzCash branding
• Cloned login pages replicating mobile wallet interfaces
• Hosting environments capable of rapidly deploying phishing assets
• Coordinated domain clusters supporting campaign scalability
Such infrastructure allows attackers to launch multiple phishing pages simultaneously, increasing the chances that some will evade detection and reach victims.
By mapping relationships between these infrastructure components, PhishReaper was able to identify the broader phishing ecosystem supporting the campaign.
This infrastructure-level intelligence provides security teams with deeper visibility into how phishing campaigns operate behind the scenes.
Why Mobile Payment Platforms Are Attractive Targets
Digital payment platforms such as JazzCash represent highly attractive targets for cybercriminals.
These platforms handle:
• Financial transactions
• Personal identification information
• Mobile authentication credentials
• Linked bank accounts and wallets
Because users frequently interact with these platforms via SMS messages, mobile notifications, and web links, phishing campaigns can easily exploit these communication channels.
Attackers often create phishing pages that mimic account alerts, payment confirmations, or reward campaigns, messages that encourage users to interact quickly without verifying authenticity.
This social engineering tactic significantly increases the success rate of phishing attacks.
Why Traditional Security Systems Often Miss These Campaigns
Many traditional cybersecurity solutions rely on reactive detection mechanisms that depend on known indicators of compromise.
These systems typically detect phishing threats only after:
• Victims report suspicious links
• Security researchers identify malicious pages
• Domains appear on public blocklists
Such detection models introduce delays between the launch of a phishing campaign and its eventual discovery.
In large-scale phishing campaigns like the JazzCash operation, attackers may exploit this delay to distribute malicious links widely before detection systems respond.
As phishing infrastructure becomes more automated and scalable, reactive detection alone is increasingly insufficient.
PhishReaper’s Infrastructure-Level Threat Hunting
PhishReaper approaches phishing detection through intent-driven infrastructure analysis.
Instead of waiting for phishing pages to be reported, the platform analyzes signals that indicate a domain was created specifically for malicious purposes.
This includes examining:
• Suspicious domain naming patterns
• Brand token abuse
• Infrastructure relationships between domains
• Attacker deployment patterns
By identifying these signals early, PhishReaper can detect phishing infrastructure before it becomes widely visible across traditional threat-intelligence channels.
In the JazzCash case, this proactive analysis enabled investigators to identify a broader phishing ecosystem rather than focusing on isolated malicious pages.
Strategic Implications for Fintech and Telecom Ecosystems
Phishing campaigns targeting mobile payment services pose significant risks for both organizations and their customers.
Brand-abuse attacks can lead to:
• Theft of financial credentials
• Unauthorized transactions
• Identity theft
• Reputational damage for payment platforms
For fintech providers and telecom operators operating mobile wallet ecosystems, early detection of phishing infrastructure is essential to protecting users and maintaining trust.
Proactive threat-hunting platforms such as PhishReaper allow organizations to identify phishing campaigns earlier and respond before large-scale fraud occurs.
Moving Toward Proactive Cyber Defense
The JazzCash phishing operation highlights a broader trend within the cybersecurity landscape: phishing campaigns are evolving into structured, scalable operations.
Rather than deploying a single malicious website, attackers now build infrastructure capable of supporting mass-phishing activity across multiple channels.
To counter this threat, organizations must adopt proactive detection strategies capable of identifying malicious infrastructure before campaigns reach widespread distribution.
Such technologies provide:
• Earlier visibility into phishing operations
• Stronger protection against brand impersonation
• Deeper understanding of attacker infrastructure
• Enhanced threat-intelligence capabilities for SOC teams
This shift from reactive detection to proactive threat hunting represents a critical step in modern cybersecurity defense.
Conclusion
The JazzCash brand-abuse campaign uncovered by PhishReaper demonstrates how phishing operations targeting digital payment platforms can evolve into large-scale, coordinated attacks.
By analyzing the infrastructure supporting the campaign, PhishReaper’s threat-hunting technology was able to illuminate a mass-phishing ecosystem designed to impersonate a trusted financial service.
This investigation reinforces the importance of proactive phishing detection and infrastructure-level threat intelligence.
Through its collaboration with PhishReaper, LogIQ Curve remains committed to helping organizations identify phishing campaigns before they escalate into major cyber incidents.
Learn More About PhishReaper
Organizations interested in evaluating the PhishReaper phishing detection platform can contact LogIQ Curve to learn how this technology can strengthen enterprise security operations.
📧 security@logiqcurve.com
LogIQ Curve works with:
• Banks
• Telecom operators
• Government organizations
• Enterprises
• SOC teams
to identify phishing infrastructure before attacks, reach users.
Research Attribution
This analysis is based on the original threat-intelligence research conducted by PhishReaper. LogIQ Curve republishes these findings for its global audience as the Exclusive OEM Partner of PhishReaper in Pakistan, helping organizations gain early visibility into emerging phishing threats. (PhishReaper)
Description
PhishReaper uncovers a mass-phishing campaign abusing the JazzCash brand. Discover how proactive threat hunting exposed the infrastructure behind this large-scale fintech phishing operation.
#PhishReaper #LogIQCurve #CyberSecurity #PhishingDetection #ThreatIntelligence #ThreatHunting #CyberDefense #EnterpriseSecurity #SOC #AIinCybersecurity #DigitalSecurity #CyberResilience #FintechSecurity #MobileWalletSecurity #InfoSec #SecurityOperations #CyberThreats #PakistanCyberSecurity #CyberInnovation #SafwanKhan #HaiderAbbas #NajeebUlHussan #MumtazKhan #CISO #CTO #SecurityLeadership