Introduction to Modern SOC Challenges
The Explosion of Cyber Threats in 2025–2026
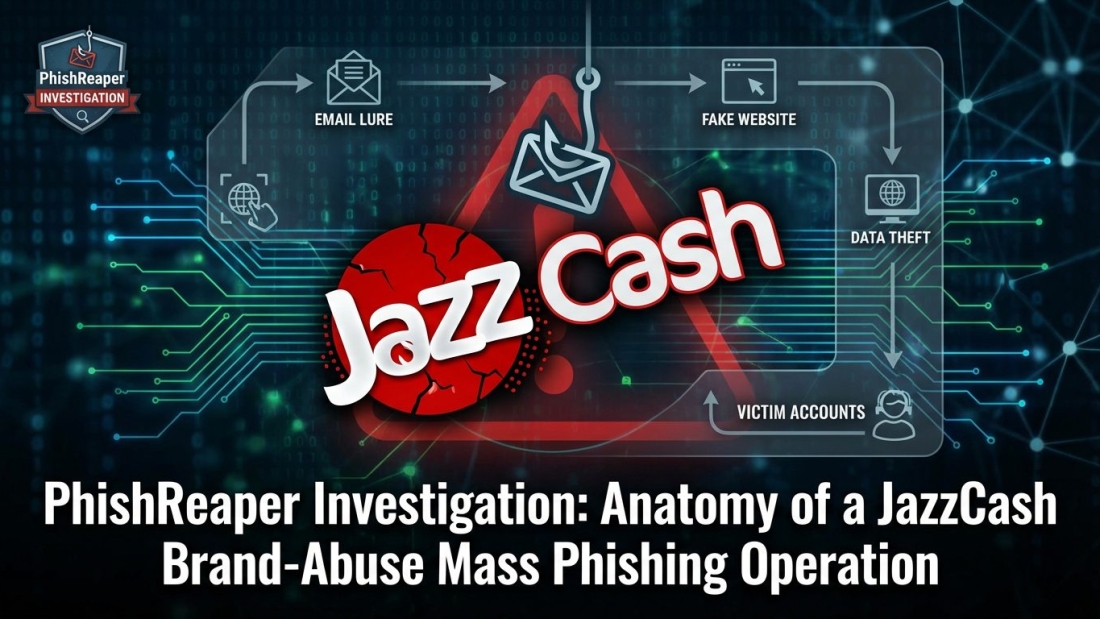
Cybersecurity today feels like trying to stop a flood with a bucket. Every day, organizations are dealing with a massive surge in cyberattacks, and the scale keeps growing. On average, companies now face thousands of attacks weekly, and the sophistication of those attacks has increased dramatically. What makes it even more intense is the role of artificial intelligence in fueling this growth. Attackers are no longer relying solely on manual techniques; they are using AI to automate their efforts, generate convincing phishing campaigns, and identify vulnerabilities faster than ever before.
Think of it like this: earlier, cybercriminals were working like individual hackers testing systems manually. Now, they are running automated factories of attacks that never sleep. This shift has made the cybersecurity landscape more aggressive and unpredictable. AI-driven threats can adapt quickly, making them harder to detect using traditional systems. This creates a serious challenge for enterprise Security Operations Centers, which are expected to defend against these evolving threats with limited resources.
Because of this rapid escalation, organizations can no longer rely on slow, manual processes. The speed of modern attacks demands faster detection and response. If a threat can infiltrate a system within minutes, a delayed response could mean significant financial and reputational damage. This is why AI-assisted threat detection is no longer optional; it has become a critical component in modern cybersecurity strategies.
Why Traditional SOC Models Are Breaking Down
Traditional SOC models were designed for a different time, when threats were less frequent and easier to manage. Back then, security teams could manually review logs, investigate alerts, and respond to incidents without being overwhelmed. Today, that approach simply does not work anymore. The volume of data generated by modern IT environments is enormous, and manually analyzing it is like searching for a needle in a haystack.
One of the biggest problems is alert overload. SOC teams receive thousands of alerts daily, and a large percentage of them turn out to be false positives. This creates a situation where analysts spend a significant amount of time chasing alerts that do not matter. Over time, this leads to fatigue, frustration, and even burnout. When analysts are overwhelmed, the chances of missing a real threat increase significantly.
Another issue is the shortage of skilled cybersecurity professionals. Organizations struggle to find and retain qualified talent, which puts additional pressure on existing teams. Hiring more people is not always a feasible solution, especially for companies with limited budgets. As a result, SOC teams are expected to do more with less, which is not sustainable in the long run.
The traditional approach of scaling teams to handle increased workloads is no longer effective. Instead, organizations need to rethink how SOCs operate. This is where AI-assisted threat detection comes into play, offering a smarter and more efficient way to manage security operations.
Understanding AI-Assisted Threat Detection
What AI in Cybersecurity Actually Does
AI in cybersecurity acts like a highly skilled analyst that can process massive amounts of data in real time. Instead of relying on predefined rules, AI systems learn from data patterns and adapt over time. This allows them to detect unusual behavior that may indicate a potential threat. For example, if a user suddenly accesses sensitive data at an unusual time or from a different location, AI can flag this activity as suspicious.
What makes AI powerful is its ability to analyze data at a scale that humans simply cannot match. It can process millions of events per second, identifying patterns and anomalies that would otherwise go unnoticed. This helps organizations detect threats earlier and respond more effectively. Early detection is crucial because it reduces the potential impact of an attack.
Another important aspect of AI is its ability to improve continuously. As it processes more data, it becomes better at distinguishing between normal and abnormal behavior. This reduces the number of false positives and increases the accuracy of threat detection. Over time, this leads to a more efficient and reliable security system.
AI also enables a shift from reactive to proactive security. Instead of waiting for an attack to occur, organizations can use AI to identify potential threats before they become serious incidents. This proactive approach is essential in today’s fast-paced threat landscape.
Key Technologies Powering AI Detection
Several technologies work together to enable AI-assisted threat detection. Machine learning is one of the most important components. It allows systems to learn from historical data and identify patterns that indicate potential threats. Behavioral analytics is another key technology, focusing on understanding how users and systems normally behave and detecting deviations from that behavior.
Natural language processing plays a role in analyzing unstructured data, such as logs and reports. This helps security teams make sense of large volumes of information quickly. Automation is also a critical element, enabling systems to respond to threats without human intervention. For example, an AI system can automatically isolate a compromised device or block a suspicious IP address.
These technologies combine to create a powerful defense system that can operate at high speed and scale. By leveraging AI, organizations can enhance their ability to detect and respond to threats, even with limited resources.
Why Enterprises Need Lean SOC Teams Today
Budget Constraints and Talent Shortage
Organizations today are under constant pressure to optimize costs while maintaining strong security. Building large SOC teams is expensive, and finding skilled professionals is becoming increasingly difficult. This creates a situation where companies must find ways to operate efficiently without compromising security.
A lean SOC team focuses on maximizing productivity with minimal resources. Instead of relying on a large number of analysts, organizations use advanced tools to handle repetitive tasks. AI plays a crucial role in this approach, acting as a force multiplier that enhances the capabilities of human analysts.
By leveraging AI, smaller teams can manage workloads that would traditionally require larger teams. This not only reduces costs but also improves efficiency. Organizations can allocate resources more effectively, focusing on strategic initiatives rather than routine tasks.
This shift toward lean SOC teams is not just a trend; it is a necessity. As threats continue to grow in complexity and volume, organizations need smarter ways to manage their security operations.
The Problem of Alert Fatigue
Alert fatigue is one of the biggest challenges faced by SOC teams. When analysts are bombarded with thousands of alerts, it becomes difficult to prioritize and respond effectively. Over time, this leads to decreased productivity and increased stress.
AI helps address this issue by filtering and prioritizing alerts. Instead of presenting every possible alert, AI systems focus on those that are most likely to represent real threats. This reduces noise and allows analysts to focus on high-priority tasks.
By reducing alert fatigue, AI improves both efficiency and job satisfaction. Analysts can work more effectively, making better decisions and responding to threats more quickly. This creates a more sustainable and productive work environment.
How AI Transforms SOC Operations
Intelligent Alert Triage and Reduction
AI significantly improves the process of alert triage. By analyzing context and patterns, it can determine which alerts require immediate attention and which can be ignored. This reduces the number of false positives and ensures that analysts focus on real threats.
This transformation is similar to having a smart filter that removes unnecessary noise from your workflow. Instead of being overwhelmed by alerts, analysts can concentrate on meaningful tasks. This leads to faster response times and better outcomes.
Automated Threat Hunting and Response
AI enables automated threat hunting, allowing systems to proactively search for potential threats. Instead of waiting for alerts, AI continuously monitors activity and identifies suspicious behavior. When a threat is detected, it can take immediate action, such as isolating affected systems or blocking malicious activity.
This level of automation is crucial in modern cybersecurity. It reduces response times and minimizes the impact of attacks. By handling routine tasks automatically, AI frees up analysts to focus on more complex challenges.
Core Benefits of AI-Assisted SOCs
Faster Detection and Response Times
Speed is a critical factor in cybersecurity. AI allows organizations to detect and respond to threats in real time, reducing the potential impact of attacks. Faster response times mean less damage and lower recovery costs.
Reduced Burnout and Improved Efficiency
By automating repetitive tasks, AI reduces the workload on analysts. This leads to improved efficiency and lower stress levels. Analysts can focus on strategic tasks, making better use of their skills and expertise.
Building a Lean SOC Team with AI
Redefining Roles in the SOC
AI changes the roles within a SOC. Analysts shift from manual tasks to overseeing and managing AI systems. This requires new skills and a different approach to security operations.
Human + AI Collaboration Model
The combination of human expertise and AI capabilities creates a powerful defense system. AI handles data processing and routine tasks, while humans provide context and decision-making. This collaboration enhances overall effectiveness.
Tools and Technologies for AI-Driven SOC
SIEM, SOAR, and XDR Evolution
Modern security tools are evolving to incorporate AI capabilities. SIEM systems are becoming more intelligent, while SOAR and XDR platforms focus on automation and integration. These tools work together to create a unified security ecosystem.
AI Copilots and Automation Platforms
AI copilots assist analysts by providing insights and recommendations. They act as virtual assistants, helping teams make informed decisions quickly.
Challenges of AI in SOC Environments
Data Quality and False Positives
AI systems rely on high-quality data. Poor data can lead to inaccurate results, making it essential to maintain clean and reliable datasets.
Trust, Explainability, and Compliance
Organizations need to ensure that AI decisions are transparent and understandable. This is especially important in regulated industries where compliance is critical.
Best Practices for Implementation
Start Small, Scale Smart
Organizations should begin with specific use cases and gradually expand AI capabilities. This approach reduces risk and ensures successful implementation.
Focus on Use Cases with Immediate ROI
Prioritizing high-impact use cases helps organizations achieve quick wins and justify further investment in AI.
The Future of SOC Teams in the AI Era
The future of SOC teams lies in combining human expertise with AI capabilities. Lean teams equipped with advanced tools will be able to handle complex threats more effectively. This approach ensures that organizations can stay ahead of evolving cyber threats while optimizing resources.
Conclusion
AI-assisted threat detection is transforming the way SOC teams operate. By enhancing efficiency, reducing workloads, and improving response times, AI enables organizations to build lean yet highly effective security teams. This shift is essential in a world where cyber threats are becoming more sophisticated and frequent.