A Strategic Turning Point in Cyber Defense
From Reaction to Anticipation
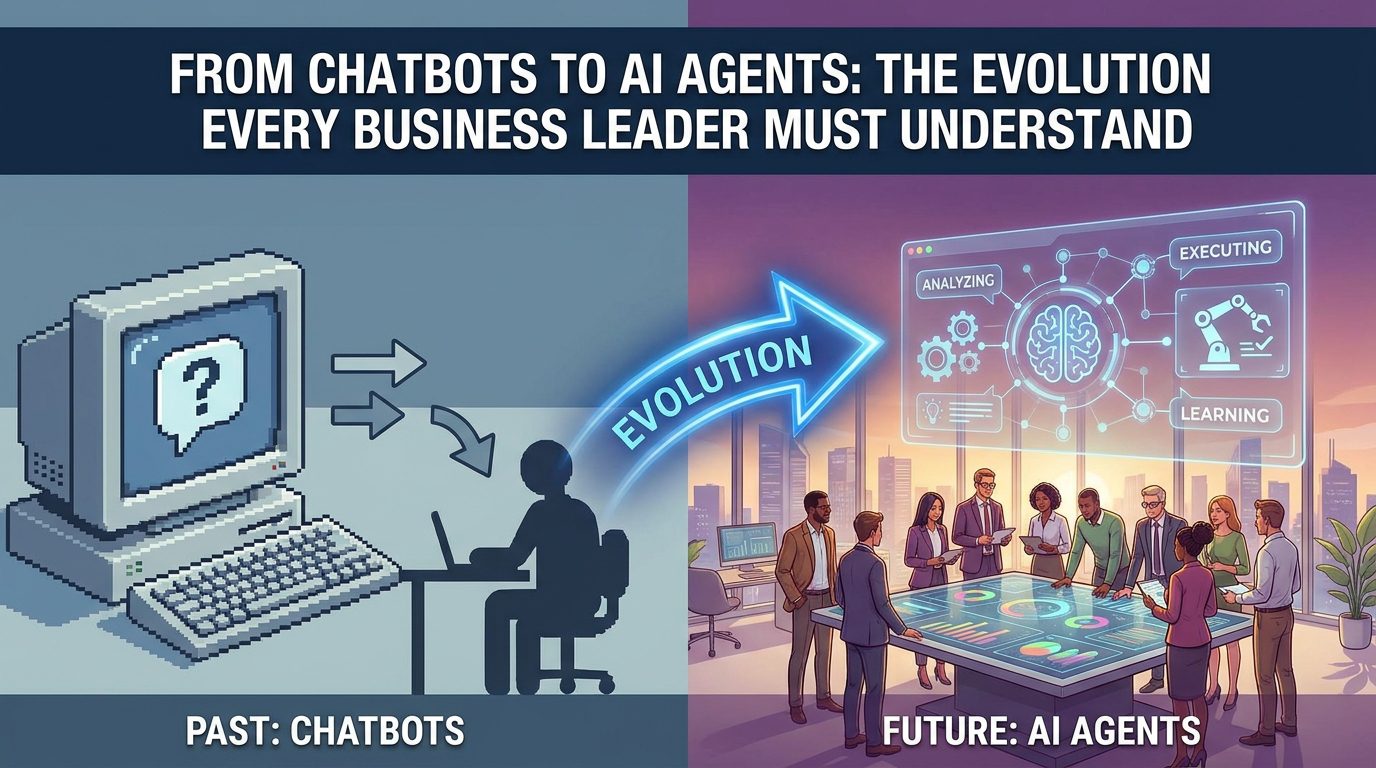
Cybersecurity has undergone a quiet yet profound metamorphosis. Not long ago, most digital defenses were engineered with a reactive mindset—systems would lie dormant until a threat surfaced, then scramble to respond. Firewalls and antivirus programs functioned much like sirens in the night, alerting administrators only after something had already gone awry. That model once sufficed, when cyber intrusions were slower, more predictable, almost mechanical in nature.
Fast forward to 2026, and the landscape feels almost unrecognizable. Threat actors have evolved into agile tacticians, wielding sophisticated tools that operate at blistering speed. Relying on a reactive stance today is akin to chasing shadows—you’re always a step behind. Businesses are now pivoting toward a more anticipatory posture, one that neutralizes threats before they even take shape. This is no passing fad; it’s a survival instinct in a hyper-connected ecosystem.
The Fragility of Detection-Centric Models
Detection systems hinge on familiarity. They sift through activity, hunting for patterns that mirror known threats. But here’s the paradox—modern attackers thrive on novelty. They mutate their methods constantly, crafting exploits that bear little resemblance to anything previously cataloged.
This creates a perilous blind spot. When an attack doesn’t match an existing signature, it simply glides past unnoticed. Leaning solely on detection, therefore, feels like navigating uncharted terrain with an outdated compass. Occasionally helpful, yes—but dangerously insufficient when the terrain itself keeps shifting.
Decoding Pre-emptive Cybersecurity
A Philosophy Rooted in Foresight
Pre-emptive cybersecurity flips the script entirely. Instead of reacting to breaches, it endeavors to foresee them. It’s about identifying latent vulnerabilities, interpreting subtle behavioral shifts, and dismantling risks before they crystallize into full-blown attacks.
Picture a vigilant sentinel—not just guarding the gates, but studying the rhythm of the surroundings, recognizing anomalies, and intercepting danger long before it arrives. That’s the essence of this approach. It thrives on foresight, fueled by data, sharpened by intelligence, and executed through automation.
The Structural Pillars
At its foundation, pre-emptive security is an orchestration of several critical elements:
- Threat intelligence, which deciphers emerging dangers before they mature
- Behavioral analytics, capable of spotting deviations that hint at compromise
- Automated response mechanisms, ensuring immediate action without hesitation
- Perpetual monitoring, maintaining an unbroken watch over digital ecosystems
Together, these components form a living, breathing defense system—one that adapts, learns, and evolves continuously.
Why Detection Alone Is Crumbling
The Velocity Dilemma
Modern cyberattacks unfold with startling سرعت—sometimes within mere seconds. By the time a detection system raises an alert, the breach may already be complete. Sensitive data siphoned, systems immobilized, operations disrupted—all before a human can even blink.
This temporal mismatch renders traditional detection mechanisms increasingly obsolete when used in isolation. Organizations now require defenses that don’t just observe but intervene instantly.
The Enigma of the Unknown
Perhaps the most insidious threat comes from the unknown—zero-day vulnerabilities that lurk beneath the surface, undiscovered and unpatched. Detection systems, bound by their reliance on historical data, remain oblivious to these hidden fractures.
Pre-emptive cybersecurity sidesteps this limitation by focusing on irregularities rather than predefined signatures. When behavior deviates from the norm, alarms are triggered—even if the threat itself has never been seen before. It’s a shift from recognition to intuition.
Technological Catalysts Behind Pre-emptive Security
Artificial Intelligence and Autonomous Action
Artificial intelligence has become the cerebral engine of modern cybersecurity. It digests colossal volumes of data, identifies intricate patterns, and draws conclusions at a pace no human could replicate. More importantly, it doesn’t just analyze—it anticipates.
Automation complements this intelligence by eliminating latency. Decisions are executed in real time, without waiting for manual intervention. The fusion of AI and automation creates a defense mechanism that is both swift and sagacious.
Behavioral Surveillance
Behavioral monitoring introduces a different lens. Instead of asking, “Is this threat known?” it asks, “Does this behavior feel right?” It observes the habitual patterns of users and systems, building a baseline of normalcy.
When deviations occur—say, an unusual login attempt or an unexpected data exfiltration—the system reacts instantly. This anomaly-driven approach proves invaluable against novel and evolving threats.
Weighing the Gains Against the Hurdles
The Upside
The advantages of pre-emptive cybersecurity are compelling. It dramatically lowers the probability of successful intrusions, safeguards sensitive assets, and curtails operational disruptions. Organizations gain not just protection, but peace of mind.
There’s also an efficiency dividend. With automated systems handling routine surveillance and response, human teams are liberated to focus on strategic, high-value tasks rather than firefighting endless alerts.
The Roadblocks
Yet, the journey toward pre-emptive security is not without friction. The financial investment can be substantial, particularly for smaller enterprises. Advanced tools, skilled personnel, and infrastructure upgrades all demand resources.
Additionally, there’s a cognitive shift required. Teams must acclimate to new technologies, rethink established workflows, and embrace a more dynamic security philosophy. It’s a transformation that takes time—but one that pays dividends in resilience.
Practical Deployments in the Real World
Enterprise Landscapes
Large-scale organizations have already begun weaving pre-emptive strategies into their security fabric. Leveraging AI-driven platforms, they monitor network गतिविधि, detect subtle anomalies, and thwart attacks before they materialize. This proactive stance not only protects data but also fortifies trust among stakeholders.
The Cloud Conundrum
As businesses migrate to cloud environments, the attack surface expands exponentially. Pre-emptive cybersecurity rises to this challenge by maintaining continuous vigilance, ensuring that distributed systems remain secure despite their complexity. Real-time risk mitigation becomes the norm rather than the exception.
Looking Ahead
Cybersecurity in 2026 is no longer a game of reaction—it’s a discipline of anticipation. The era where detection alone could suffice has quietly faded into obsolescence. In its place stands a more nuanced, intelligent paradigm—one that prioritizes foresight over hindsight.
Organizations that embrace this evolution position themselves not just to survive, but to thrive in an unpredictable digital भविष्य. Those that cling to outdated models risk being outpaced, outmaneuvered, and ultimately overwhelmed.
The verdict is unmistakable: waiting for threats to appear is no longer a viable strategy. The future belongs to those who can see them coming.